1. How Much Does Your ERP Really Cost to Support?
The median number of users per ERP support staff member is 31. Several months ago, I recommended that you check out Frank Scavo's 10-minute survey on ERP support costs. Frank is the President of Computer Economics, an IT research and advisory firm, and he also writes the Enterprise System Spectator (http://fscavo.blogspot.com). Now that Frank has compiled the results, here's what he has to say:
"The median number of users per ERP support staff member is 31, across organizations of all sizes and all types of systems. However, this figure masks the variation that is introduced in the support staff ratio by a number of factors: size and age of the installation, vendor, extent of code modification, and number of versions and instances in production. Our study analyzes the effect of these factors on support requirements, and also breaks down the support staff into detailed job functions, such as programmers, business analysts, project managers, DBAs, help desk personnel, and other support positions."
The full report can be purchased at http://www.computereconomics.com/article.cfm?id=1325, and an executive summary can be read at http://www.computereconomics.com/article.cfm?id=1328.
2. How Well Does Lawson Support You?
While we're on the topic, let's tackle one of my perennial favorites: Lawson Support. At the recent Lawson CUE 2008, CEO Harry Debes laid out three overall goals for the continuing improvement of Lawson Support:
- Timeliness
- Accuracy
- Professionalism
To those, I'd like to add "predictability" and "consistency". My personal experience on recent calls has been that it really depends on who takes your case; in some cases, I get the cream-of-the-crop, who always works the issue through to a successful conclusion, usually issuing a PT, and then even following up to let me know when the CTP is available. In other cases, however, it's seems like they're just going through the motions. I just love knowing when the LIS consultant is going to lunch, and "didn't have time to work on your issue, I'm going home, and I'll try to work on it tomorrow".
You've no doubt received one of those follow-up calls after a support case has been concluded, asking survey questions about your level of satisfaction with Lawson Support--but they only allow you to answer regarding that particular case. And, it naturally seems like you only get one of those follow-up calls when it's a case with has a happy ending.
Send your comments (both good and not so good) to letter-comments@lawsonguru.com, and we can share some highlights (anonymously of course) about how how well you think Lawson Support is really doing.
3. ProcessFlow Integrator, Part 4: Introducing the Nodes
Moving further into this article series, we’re starting to dig a little deeper into using ProcessFlow Integrator. Refreshing your memory, you’ll remember that these are the primary components of Lawson ProcessFlow:
-
ProcessFlow Server: The “engine” that executes flows which you have developed and deployed to the server. This component is installed as part of LSF9, and runs on the Lawson Application Server: There is a small command-line utility, called pfserv, which you run on the server to configure ProcessFlow.
-
Event Management Console: Desktop component used to manage ProcessFlow server and log files.
-
Scheduler: This component is a desktop component which works in conjunction with the ProcessFlow Server, for time-based initiation of flows.
-
Administrator: Desktop component for managing Work Units associated with flows, and capture details; also used for troubleshooting “stuck” flows.
-
Web Administration: There is a set of web-based (e.g., http://server/bpm/menu.do) forms which replace the LOGAN WFxx forms
-
ProcessFlow Designer: This is the desktop tool you use to actually build your flows. It’s what is available to you in the Designer that makes up the different editions of ProcessFlow.
In this article we start to look at designing flows, which means using the ProcessFlow Designer. It’s in the Designer that you fasten together a collection of “Activity Nodes” to orchestrate a business process. Activity Nodes are connected together to represent logic; each Activity Node can use the output of previous Node(s) as its input (i.e. that’s what makes up the “flow”). While some Activity Nodes are self-contained (i.e. they perform a defined function), some nodes can be extended via JavaScript; Lawson supplies some functions, but you can customize to meet your own needs.
The JavaScript Foundation
ProcessFlow using variables which are built on JavaScript (more technically ECMAScript) is an object-oriented language. I won’t even attempt to explain objects in much detail. Suffice it to say that everything in JavaScript is an object.
Here are my keys to understanding JavaScript:
- Objects are grouped hierarchically and inherit from their parents.
- Objects have properties (i.e. variables or settings)
- Objects support their own methods (i.e. functions/subroutines)
- Objects invoke the methods of other objects (i.e. clicking one button fills a text box)
- Objects respond to events (i.e. “I’m a button and someone clicked me!”)
ProcessFlow uses JavaScript behind-the-scenes to manipulate the flow elements/nodes. However, it's a little different, in that you really only write procedural JavaScript--you don't respond events like you do with Design Studio.
There are tons of books and resources on the web for learning JavaScript; here are a couple: http://www.webmonkey.com/webmonkey/programming/javascript/tutorials/tutorial1.html http://www.webreference.com/programming/javascript/definitive/
I also recommend looking at Lisa Wollin's excellent blog tutorials about JavaScript and the object models:
http://blogs.msdn.com/lisawoll/archive/2005/03/16/396878.aspx http://blogs.msdn.com/lisawoll/archive/2005/04/05/405744.aspx
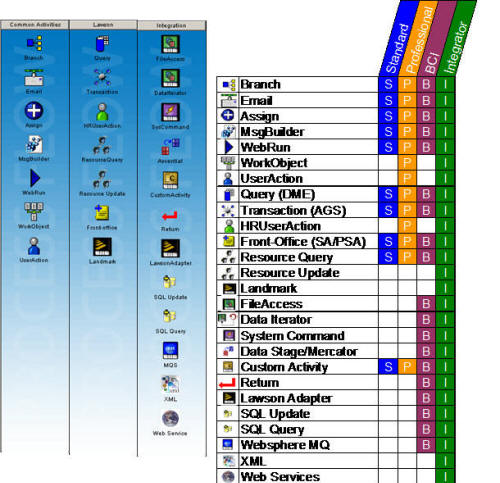
Some Basic Nodes
Within the ProcessFlow Designer, there are over 25 built-in activities available for you to use to perform workflow and integration functions. With this article, and some future ones, we will look in more detail at each of the nodes. Remember that which Activity Nodes you have available to you depends on which edition of ProcessFlow you own.
Start and End
Every flow in ProcessFlow needs to have a starting point and an ending point; hence the two absolutely required nodes: Start and End. In fact you can’t remove them, and your flow won’t run without them:
Remember that Activity Nodes are connected together to represent logic; each Activity Node can use the output of previous Node(s) as its input (i.e. that’s what makes up the “flow”). One of the most important aspects of the Start node is that it is used to define process-wide variables, which you can reference later on during your flow:
 The Assign Node
The Assign Node

(Note: As we work our way through an explanation of each node, you will see that I’ve included a key (S-P-B-I) to signify which ProcessFlow editions include that node.)
As you are designing your flow, you will need to access and manipulate the variables (which have defined in your flow via the Start node) using the Assign node:
Once you’re in the Assign node, you use the left and right “chevrons” to assign simple values to your variables:
You can also click the ‘JavaScript Expression’ button (or double-click an existing expression):
This opens up a JavaScript Expression Builder, where you can put any sort of JavaScript logic you need to include in your flow:
Lawson delivers a number of predefined JavaScript functions with ProcessFlow, particularly for date/string handling. You can also define your own, which might be specific to your organization, and also promotes code re-use. To do that, you modify the ‘pflow.js’ file, which is installed with the Designer on your machine, and also will need to be copied to your server.
Note that you will definitely want to keep a backup of your pflow.js if you add functions, because subsequent ProcessFlow patches/updates will overwrite the file.
 The Branch Node
The Branch Node

Something nearly all flows need to do is to make decisions, execute different logic depending on conditions encountered in the flow. In this example, a Branch node is used to create and send an email message if errors are encountered in the previous AGS node:
Branches are defined using JavaScript-based conditions which are based on the connection between the Branch node and its successors:
Each condition is evaluated consecutively, until a match is made. So, you’d typically have more than one condition:
The Branch node allows you to represent IF-ELSE or “switch”-type scenarios using JavaScript expressions, access outputs from previous Activity Nodes as JavaScript variables. Like the Assign node, the Branch node supports JavaScript syntax as well as the Lawson-delivered (and/or client-built) functions.
 Message Builder Node
Message Builder Node

The Message Builder node takes input from other variables and aggregates them into resulting variable. Using this node you can collect data from looping-type Activity Nodes into a variable:
Another way you can use the Message Builder node is to create simple “reports”, which typically then feed into a subsequent Email node:
 Email Node
Email Node

Well, it’s pretty obvious, you use it to send emails. Messages can be sent to specific email addresses, or you can route to ProcessFlow tasks or users defined in Lawson Resource Management. The “from”, “to”, “cc”, and “bcc” fields as well as the email body can include ProcessFlow variables, so you don’t have to “hard-code” anything. You can also attach documents (stored on the Lawson application server), and with LSF9, you can send HTML content:
4. Worthwhile Reading
How to Get Real About Strategic Planning
Everyone agrees that having a strategic plan for IT is a good thing but most CIOs approach the process with fear and loathing. In fact, the majority of CIOs (and the enterprises they work for) are faking it when it comes to strategic planning. Isn't it time we all got real?
- QUOTE OF THE ISSUE –
“Energy and persistence conquer all things.”
-- Benjamin Franklin
CIO Magazine, January 18, 2008
http://www.cio.com/article/173600
A New Vision for Accounting
Robert Herz and FASB are preparing a radical new format for financial statements.
CFO Magazine, February 2008
http://www.cfo.com/article.cfm/10597001/c_10598910
Linking BI and Process Management
Linking business intelligence (BI) and business process management (BPM) creates stronger operational business intelligence (OBI). As organizations move from developing cubes and management reports towards scorecards, dashboards and real-time BI, the way BI is used is transformed into a proactive decision-making tool.
BI Review, February 28, 2008
http://www.bireview.com/bnews/10000932-1.html
5. Lawson Tips & Tricks
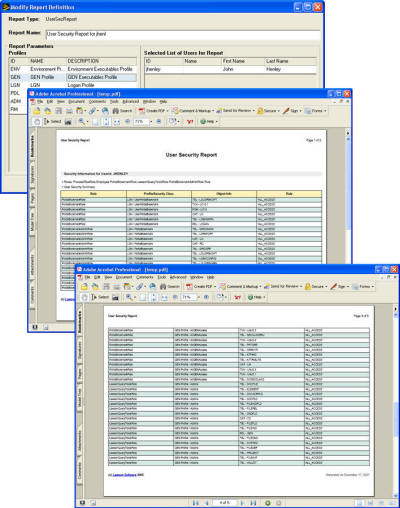
LSF9 Application Security Reports
One of the oft-overlooked tools you can use to troubleshoot and document Lawson S3 9.0 Applications Security in LSF9 is to use the new reports. One of the ones that I find particularly useful is the User Security Report, which shows all of the securable objects a user can access, and why (i.e. which role/class):